Understanding the NIS2 Directive: A Comprehensive Overview of new Cybersecurity Directive by EU

The NIS2 Directive, part of the European Union’s cybersecurity framework, strengthens security measures for critical infrastructure. It was adopted on January 16, 2023, to enhance requirements for cybersecurity, reporting, and crisis management. Compliance with NIS2 is mandatory for businesses in the EU to protect their systems and mitigate cyber threats.
NIS2, short for “Network and Information Security Directive 2” builds upon its predecessor, NIS.
Here are some of the key changes when transitioning from the NIS to the NIS2 Directive:
- Expanded Scope: NIS2 broadens its reach to cover more sectors and digital service providers, including essential and important entities in areas like public administration, energy, and transportation.
- Proactive Compliance: Regulatory bodies now expect regular engagement and reporting from entities in critical sectors to ensure cybersecurity compliance.
- Increased Accountability: NIS2 holds organizational management and executives accountable for cybersecurity, not just security teams.
- Mandatory Compliance: Essential and important entities must manage cybersecurity risks, report incidents, and protect data.
Other fundamental changes include data security governance, third-party risk management, and information sharing.
NIS2 Directive comprises of 46 articles structured on Five security Pillars to achieve Three Core Objectives. | |
Core Objectives of NIS2 |
|
Pillars of NIS2 |
|
APPLICABILITY OF NIS2 DIRECTIVE:
With NIS 2 the number of sectors covered by the directive will be expanded from seven to 18, with over 160,00 businesses estimated to fall under the new directive, these are further divided into the two following tiers as listed in Annexes I and II of the Directive: Essential entities, comprising the seven-sector covered by NIS 1, including Transport, Banking, Finance, Health, energy, Digital Infra and Drinking Water, as well as three additional sectors (public administration, wastewater, space). Important entities, including post services, Space, Digital food manufacturing and distribution, Digital media Providers and chemical production.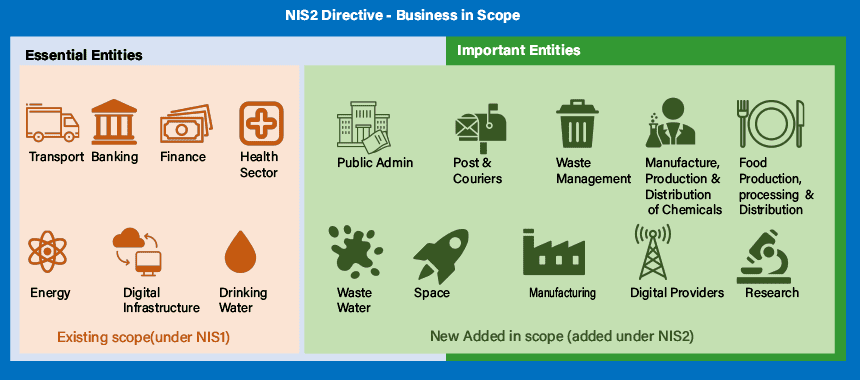
REGISTRATION OF ESSENTIAL AND IMPORTANT ENTITIES
The final registration process and the required information will be outlined during the transposition of the Directive into law. By April 17, 2025, Member States must identify the essential and important entities covered by the NIS2 Directive. Entities may be allowed to self-register.
Therefore, entities must determine if their services fall within the scope of NIS2, identify the Member States where they provide services, and register before the deadline in each Member State.
Registration will include providing at least the following details:
- Name, address, and registration number
- Sector or sub-sector falling under NIS2 scope
- Updated contact details
- Member states of operation
- List of assigned IP addresses
COOPERATION AT UNION AND INTERNATIONAL LEVEL
To foster strategic cooperation and information exchange among Member States and enhance trust and confidence, a Cooperation Group has been established. This group comprises representatives from Member States, the Commission, and ENISA. Additionally, two key entities have been set up to strengthen cybersecurity measures:
- CSIRTs Network: Computer Security Incident Response Team (CSIRT) network aims to boost confidence and trust while facilitating rapid and effective operational collaboration among Member States.
- European Cyber Crisis Liaison Organisation Network (EU-CyCLONe): EU-CyCLONe supports the coordinated management of large-scale cybersecurity incidents and crises at the operational level among Member States, Union institutions, bodies, offices, and agencies.
INFORMATION SHARING AND REPORTING OBLIGATIONS:
The NIS2 Directive mandates that Essential and Important entities promptly notify the competent national authorities, including the Computer Security Incident Response Team (CSIRT), of any incident that significantly impacts services in the sectors or sub-sectors. A significant incident is defined as one that:
- Causes or has the potential to cause serious operational disruptions to services or financial losses to the entity concerned, or
- Affects or has the potential to affect other individuals or entities by causing significant material or non-material damage.
When it comes to reporting incidents or even near misses, Essential entities are subject to stricter rules, requiring them to report a cyber incident within 24 hours, whereas Important entities have 72 hours to report such incidents.
For more details on reporting requirements, see Articles 23 and 30 of the NIS2 Directive, among others.
SUPERVISION AND ENFORCEMENT:
The directive mandates Member States to ensure that entities under NIS2 adhere to regulations and report incidents. National authorities are empowered to act if non-compliance occurs, including penalizing violations of risk management or incident reporting rules.
- Essential entities will pay fines of either 2% of their worldwide annual turnover recorded during the preceding financial year or €10m – whichever is higher.
- For important entities, non-compliance fines amount to the highest between 1.4% of annual turnover or €7m.
- Additionally, senior management representatives of essential entities may be held accountable for non-compliance with the obligations outlined in this Directive in order to incentivize adherence.
For full details on sanctions, see Articles 31-37 of the NIS2 Directive.
NEXT STEPS FOR ORGANISATION TO PREPARE FOR NIS2?
Proactive groundwork is essential for NIS2 compliance. This involves securing top management support, gaining stakeholders’ buy-in, and securing the necessary budget and resources. However, it’s crucial to anticipate potential delays and adhere to strict planning with firm deadlines. Additionally, implementing certain requirements can be considered as quick wins, such as establishing incident escalation and reporting processes to relevant authorities.
As organizations prepare for NIS2 compliance, several critical steps must be taken:
- Assess the Regulatory Landscape: Gain a comprehensive understanding of the regulatory framework governing your business operations.
- Evaluate Compliance Readiness: Assess your organization’s preparedness and capability to adhere to NIS2 directives.
- Test Incident Response: Proactively test incident response processes to ensure efficacy and readiness in the event of a cyber crisis.
- Integrate Resilience: Embed resilience testing as a key component of cybersecurity practices to enhance organizational readiness.
- Manage Threats and Vulnerabilities: Develop a robust end-to-end threat and vulnerability management program to address potential risks proactively.
- Review IT Supply Chain Security: Evaluate your IT suppliers, particularly those critical to your operations’ continuity.
- Foster a Cyber-Oriented Culture: Cultivate a cyber-oriented culture and promote mature information security awareness among employees.
Navigating compliance is tough for organizations, especially public sector groups with limited resources. As the NIS2 deadline nears, readiness is key.
Let Predictive help you, contact us to assess your NIS2 compliance. We’ll guide you through compliance and boost your cybersecurity.
Related Posts