 March NewsletterKeep up to date with our latest news, offers, and industry trends News That Matter |
 When will the Next Major Cyber Breach Come from Space?
The rapid expansion of satellite constellations is quietly reshaping the global attack surface. From navigation systems to communications and data flows, critical business operations now depend on infrastructure beyond Earth. A compromised satellite link doesn’t just stay in orbit, it can disrupt services, corrupt data, and impact ground operations within seconds. This isn’t a distant risk; it’s an emerging business continuity challenge. We believe the future of cybersecurity lies in the convergence of traditional IT security with space- grade protocols and resilience strategies. Securing the connection between orbit and enterprise systems is no longer optional, it’s essential.
Read more |
|
|
|
|
Recent Highlights  Stop starting from zero every audit cycle Moving to NIS2 shouldn't mean more paperwork. We’ve updated Predictive to turn your compliance into a "living system" that tracks your security posture in real-time. Start with our free NIS2 Compliance Check to see exactly where you stand to Full Update Below |  🪪 Identity Weaknesses Enable Most Breaches According to recent incident response data, 90% of cyber breaches involved preventable identity and access control weaknesses, emphasizing
the need for stronger authentication and governance. Read more |
|
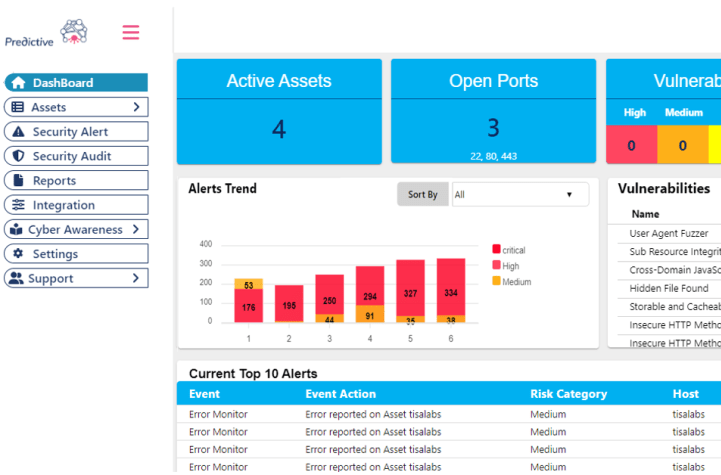
TisaLabs Cybersecurity Toolbox Automate Your NIS2 Compliance with Predictive Automating your NIS2 compliance means moving from static gap‑analysis documents to a living system that continuously builds and evidences your security posture, and this is where TisaLabs’ Predictive platform excels. Starting with TisaLabs’ free NIS2 Compliance Check to establish your current baseline, you get a clear view of where you stand today and which controls, processes, and technical measures need to improve. Once that baseline is defined, Predictive continuously scans your infrastructure for vulnerabilities, misconfigurations, and active threats, giving you real‑time visibility of the issues that most impact your NIS2 obligations. It then prioritises these findings and converts them into actionable, trackable tasks and remediation steps in your dashboard, so teams can clearly see what to fix first and how that work moves your organisation toward a higher NIS2 compliance level. Because the platform maps your evolving security posture to regulatory requirements in real time, every completed task directly feeds into your NIS2 evidence trail, simplifying audits and demonstrating ongoing risk management and “continuous improvement” demanded by the Directive. Over time, this loop, baseline via the free check, prioritised actions, tracked remediation, and live compliance mapping, lets you measurably build your NIS2 maturity instead of repeatedly starting from zero each assessment cycle.
|
|
|
|
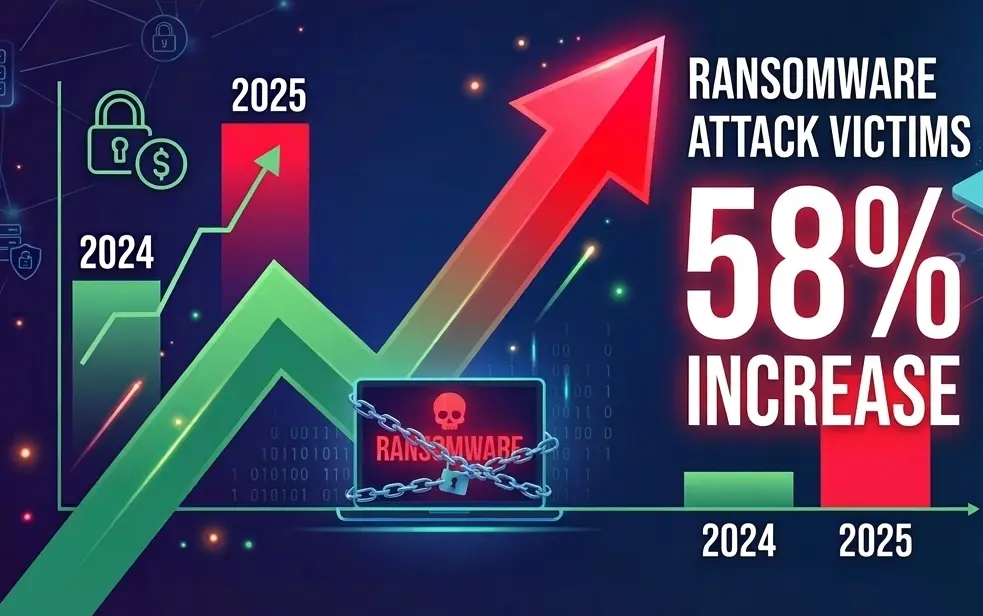
Industry Trends & Insights for 2026 🛡️📈 Ransomware Incidents Are Rising SharplyIn 2025, ransomware attack victims increased by ~58% year-over-year, making it one of the most active years ever recorded for ransomware threats. Read more
|  |
|
|
|
|
|
|
|
 | Case Study: Securing a Complex Supply Chain
How did a major energy player reduce its vulnerabilities by 40% in three months? By moving from a traditional perimeter-based defense to an Adaptive Resilience architecture. Discover our new case study on protecting data flows between critical suppliers and control centers. Learn more
|
|
|
|
|
|
|
|
|
|
|
|
|
|
TisaLabs Cybersecurity Toolbox  | Common WordPress Vulnerabilities & Security Best Practices
Did you know 98% of WordPress breaches come from outdated plugins and themes? Learn how to stay ahead of attackers and keep your site secure... Read full blog
|
|
 | Building Awareness Through Practical Learning
Continuous learning plays an important role in strengthening security posture. TisaLabs supports awareness through built-in training resources and educational webinars focused on practical cybersecurity and compliance topics. Learn more
|
|
Continued Vigilance on Emerging Threat Vectors 🛡️
| Supply Chain Attack RisksCyber attackers increasingly target software suppliers, vendors, and third-party service providers to reach multiple organizations through a single compromise. Strengthening supplier security and third-party risk management is becoming essential for modern cybersecurity programs. Read more
|  |
|
|
|
|
Need a diagnosis? Our Cyber experts are here for you
|
|
|

|
|
|
|
|
|
|
|
|
|
|
| Because technology isn’t everything, our engineering teams are available for ‘Health Check’ sessions. In just 30 minutes, we assess the robustness of your remote access and identify your critical points. Security starts with a conversation.
Book a demo
|
|